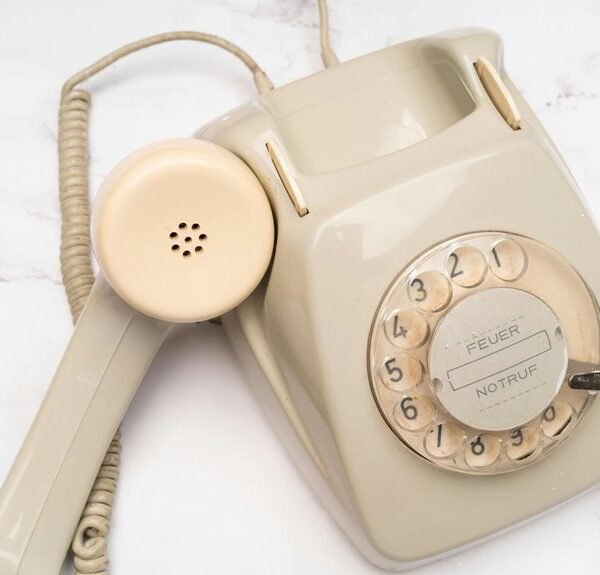
The discussion centers on a Caller Legitimacy Review related to 9567536784 and its reports. It emphasizes objective signals—data, metadata, documented outcomes—over anecdotes. The approach favors noncoercive questions, independent verification, and transparent disclosures. It notes risks of misidentification and unchecked assumptions, proposing stepwise cross-checks and third-party corroboration. If evidence remains inconclusive, actions are suspended pending corroborated data, leaving the reader with a cautious question and a need for further scrutiny.
What the 9567536784 Report Actually Reveals
The 9567536784 report presents a close examination of call data, metadata, and documented outcomes to determine whether the entity behind the number engages in legitimate activities.
Findings emphasize structured patterns over anecdotes, resisting unrelated topic and random speculation.
While indicators may suggest routine operations, gaps in disclosure invite skepticism; conclusions rely on verifiable evidence, not impressions, guarding freedom with cautious interpretation and measured uncertainty.
How to Identify Legitimate Calls vs. Red Flags
Recent findings from the prior review underscore the importance of moving beyond anecdote to assess call legitimacy through verifiable signals; this frame guides the evaluation of legitimate calls versus red flags.
The analysis prioritizes objective patterns over impression, emphasizing verifiable data, caller consistency, and corroboration.
Red flags indicate inconsistency or pressure; verification tips rely on noncoercive questions and third-party corroboration.
Steps to Verify Caller Legitimacy Quickly
Assessing caller legitimacy swiftly hinges on a standardized sequence of verifiable checks rather than impressions; by posing noncoercive, fact-seeking questions and cross-referencing responses with independent records, one can rapidly distinguish credible prompts from pressure tactics.
The method emphasizes documented identifiers, official channels, and recorded disclosures, minimizing assumptions while preserving autonomy and discernment in high-stakes interactions with unfamiliar callers.
What to Do If a Call Feels Off or Suspicious
If something about a call seems off, what steps should be taken to ground the response in verifiable measures rather than subjective impressions?
The responder should prioritize documenting caller identity, cross-checking numbers, and requesting verifiable information while avoiding concessions to emotion.
Note unrelated topic cues or stray ideas, seek independent confirmation, and suspend action until corroborated data reduces ambiguity.
Conclusion
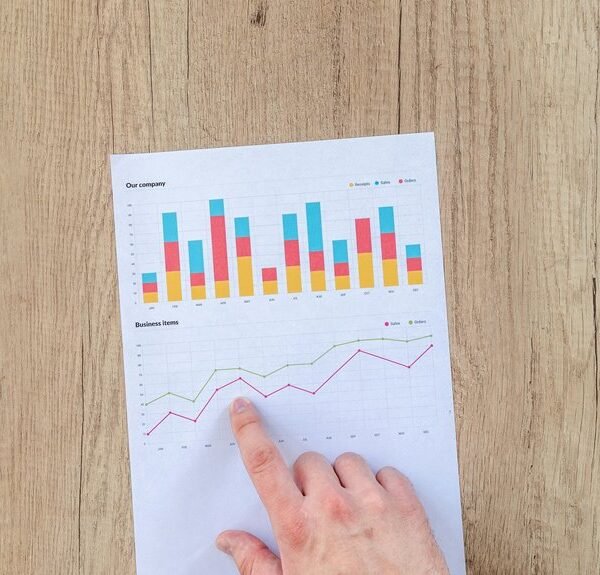
In this exhaustive, evidence-first review of 9567536784, the data stack reveals a mosaic of signals—caller metadata, call outcomes, and corroborated responses—that collectively refuse to be brushed aside. The pattern is relentlessly skeptical: no single hook confirms legitimacy, but multiple corroborations, when aligned, elevate credibility. Conversely, mismatches trigger caution. The conclusion: legitimacy is not a beacon but a balance of verifiable facts, cross-checked sources, and disciplined hesitation, never a sudden vow of trust.